CORE
Integrate the world's most advanced URL security database into your applications with simple API calls. Flexible, powerful, and built for scale.
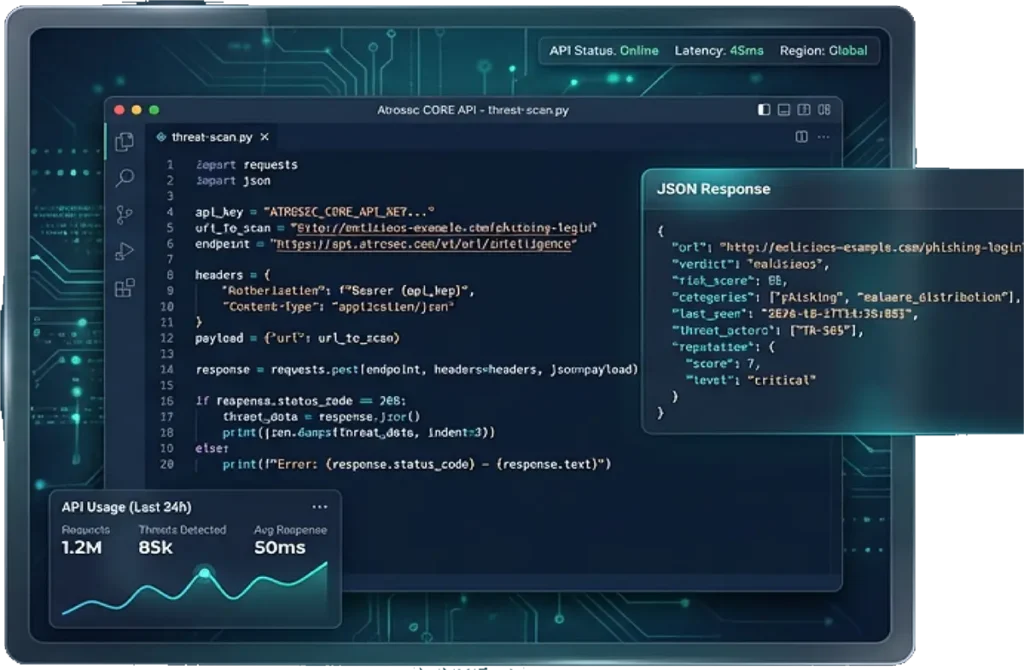
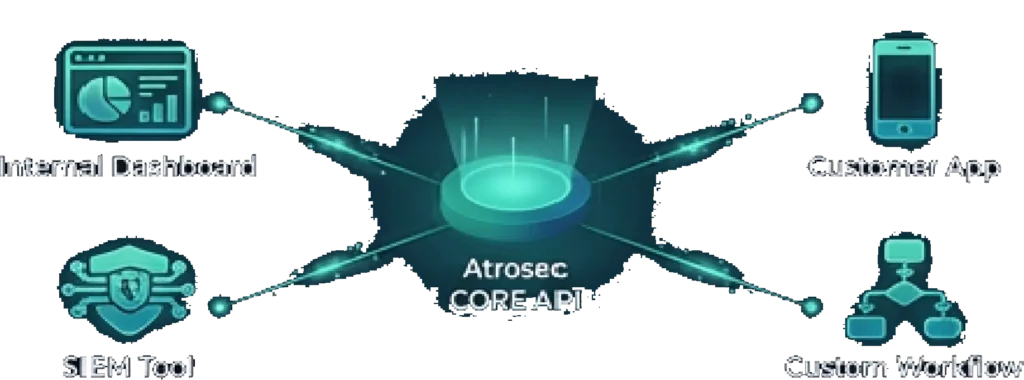
Core gives you direct access to the Atrosec MasterDB Platform—the same intelligence engine that powers our complete Trust & Safety and Telecom solutions. Whether you’re building internal security tools, enhancing existing products, or creating custom workflows, Core provides the flexibility to integrate URL threat detection exactly how you need it
Powered by Atrosec MasterDB, Core analyzes URLs in real-time using computer vision, behavioral analysis, and zero-hour threat detection. You get enterprise-grade intelligence with developer-friendly simplicity.
Perfect for security teams, product developers, and organizations that need URL threat intelligence integrated into their existing infrastructure without a pre-built dashboard or enforcement layer.
Integrate however you want—internal tools, customer-facing features, or security workflows. Your infrastructure, our intelligence.
Simple REST API with clear documentation. Get up and running in minutes, not weeks. No complex implementation required.
Access the same MasterDB intelligence used by major platforms globally. Enterprise-grade detection at any scale.
URLs are the primary attack vector for phishing, malware distribution, and fraud. Core helps you identify and mitigate these threats before they cause damage.
Problem: Sophisticated phishing links bypass traditional
filters using AI-generated lures, polymorphic URLs, and visual deception techniques.
How Core Helps:
Real-time detection with computer vision
identifies credential harvesting pages, fake
logos, and suspicious behavior patterns—even for never-before-seen URLs.
Problem: Malicious URLs deliver ransomware, trojans, and malware through obfuscated links, redirects, and time-delayed payloads.
How Core Helps:
Multi-layer analysis traces redirect chains,
scans final destinations, and identifies malware delivery mechanisms in real-time.
Problem: Attackers create fake websites impersonating your brand or trusted partners to steal credentials and damage reputation.
How Core Helps:
Visual AI detects lookalike domains, fake
login pages, and brand impersonation attempts with high accuracy—protecting your brand trust.
Problem: New threats emerge constantly. Blacklist-based solutions miss the critical first hours when
attacks are most effective.
How Core Helps:
Zero-hour detection catches threats before
they're reported or blacklisted, using behavioral analysis and visual intelligence
rather than signature matching.
users click AI-generated phishing links
average time to detect messaging-based phishing
phishing now targets platforms with user messaging
Core detects threats
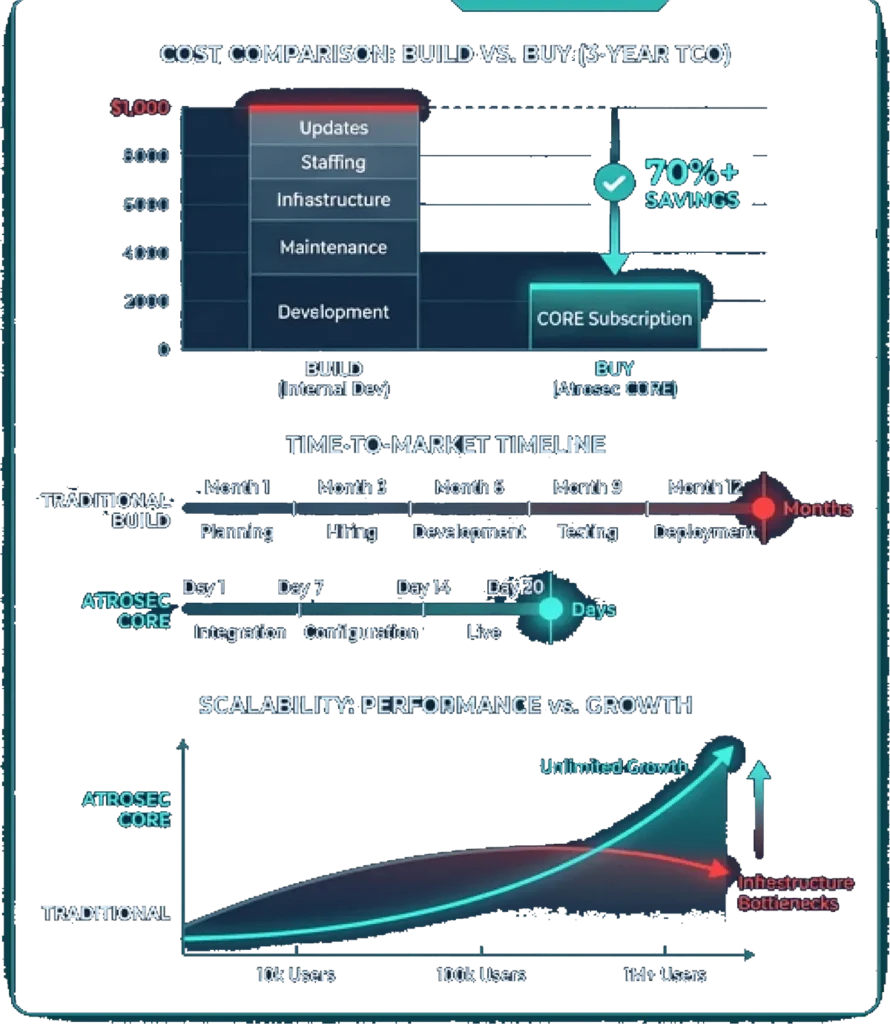
Core delivers enterprise-grade security intelligence without the overhead of building and maintaining your own threat detection infrastructure.
INSTEAD OF: Building in-house URL analysis with teams of security
researchers, maintaining threat databases, and developing ML models.
WITH CORE:
Instant access to continuously updated threat intelligence maintained by Atrosec's dedicated security team.
ROI Impact:
Save 6-12 months of development time and ongoing maintenance costs.
Pay only for what you use with flexible API pricing.
INSTEAD OF: Months of development, testing, and iteration to build
reliable URL threat detection.
WITH CORE:
Production-ready API integration in hours or days with comprehensive documentation and support.
ROI Impact:
Ship security features faster, respond to market demands immediately,
and stay ahead of competitors.
INSTEAD OF: Infrastructure scaling challenges as your user base and URL volume grows.
WITH CORE:
Built for massive scale with ultra-low latency. Handles millions of requests per second seamlessly.
ROI Impact:
Support growth without performance degradation or infrastructure complexity. No ceiling on scalability.
INSTEAD OF: Manual threat database updates, constant model retraining, and playing catch-up with new attack techniques.
WITH CORE:
Automatic access to the latest threat intelligence, detection techniques, and model improvements.
ROI Impact:
Always-current protection without additional engineering effort. Your security improves continuously without lifting a finger.
Core is designed for ease of integration with your existing infrastructure. Choose the deployment model that fits your architecture and security requirements.

WHAT IT IS: SaaS deployment with REST API endpoints. Make HTTPS requests directly to Atrosec's
secure cloud infrastructure.

WHAT IT IS: Dedicated Atrosec infrastructure in your preferred cloud region (AWS, Azure, GCP) with private connectivity.

WHAT IT IS: Self-hosted Atrosec MasterDB instance running in your data center with regular intelligence updates.
Create account and get API key instantly
Add API calls to your application code
Use sandbox environment with sample URLs
Switch to production and start protecting users
Request Body:
{
“url”: “https://suspicious-site.com/login”,
“context”: {
“user_id”: “user_12345”,
“platform”: “messaging_app”
}
}
Response:
{
“scan_id”: “89X2”,
“verdict”: “malicious”,
“risk_score”: 7,
“confidence”: “high”,
“reason”: “Credential harvesting detected”,
“indicators”: [
“fake_login_form”,
“brand_impersonation”,
“young_domain”
],
“recommendation”: “block”,
“response_time_ms”: 42
}
Get instant API access and integrate enterprise-grade URL threat intelligence in minutes. No credit card required to start.
© 2026 Atrosec. All rights reserved.