GUARD
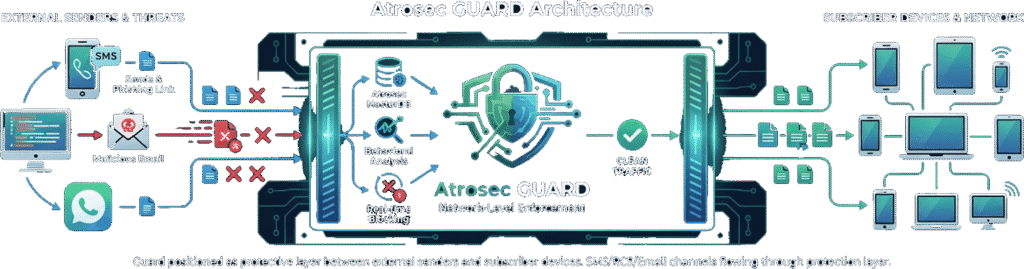
Guard blocks malicious URLs at the network level before they reach your subscribers. Protect SMS, RCS, email, and messaging channels with enterprise-grade threat intelligence.

As a telecom operator or communication service provider, you’re responsible for protecting millions of subscribers from phishing, fraud, and malware delivered through SMS, RCS, email, and messaging channels.
Guard provides comprehensive network-level enforcement powered by Atrosec MasterDB—the same intelligence engine used by major messaging platforms globally. By analyzing and blocking malicious URLs at the network layer, you protect all subscribers without requiring individual app installations or user action.
Guard acts as an intelligent firewall between external threats and your subscribers. Every URL passing through your network is analyzed in real-time with <50ms latency, ensuring legitimate messages flow freely while malicious links are blocked before delivery.
Built specifically for telecom infrastructure, Guard handles massive scale (millions of messages per second) with carrier-grade reliability, seamless integration with existing messaging infrastructure, and comprehensive reporting for regulatory compliance and network security visibility.

Protect your entire subscriber base from phishing and fraud without individual app downloads or user action.

Meet emerging anti-phishing regulations globally with demonstrable security measures and comprehensive reporting.

Gain complete visibility into threat landscape across your network with performance analytics and trend reports.
Guard solves the unique security and regulatory challenges that telecom operators and CSPs face in protecting subscribers at network scale.

THE PROBLEM: Governments worldwide are implementing strict anti-phishing regulations that hold telecom operators and financial institutions accountable for scams delivered through
communication channels.
Examples:

THE PROBLEM: Phishing and fraud delivered through SMS, RCS, and
carrier messaging erodes subscriber trust in your network. Users increasingly view carrier channels as unsafe, leading to:

THE PROBLEM: Carrier networks handle millions of messages per second. Any security solution must:

THE PROBLEM: You know threats exist on your network, but you can't see them clearly:
Powered by Atrosec MasterDB, Guard delivers comprehensive URL threat detection with the performance, reliability, and integration capabilities that telecom operators require.

WHAT IT DOES: Analyzes every URL in SMS, RCS, and email messages passing through your network in real-time. Blocks malicious links before delivery to subscribers.
KEY FEATURES:
WHAT IT DOES: Unified protection across all messaging channels
your network operates—SMS, RCS, MMS, email, and emerging messaging protocols.
KEY FEATURES:
WHAT IT DOES: Integrates with your existing telecom infrastructure without requiring major architectural changes or service disruption.
KEY FEATURES:

WHAT IT DOES: Operates with the reliability and redundancy that carrier networks demand. No single point of failure.
KEY FEATURES:
WHAT IT DOES: Comprehensive visibility into threat landscape across your network with real-time and historical analytics.
KEY FEATURES:

WHAT IT DOES: Automated reporting for regulatory compliance with comprehensive audit trails and evidence of security measures.
KEY FEATURES:

WHAT IT DOES: Flexible whitelist management for trusted senders,
legitimate marketing partners, and enterprise customers using your network.
KEY FEATURES:

WHAT IT DOES: Contribute anonymized threat data to improve global threat detection while benefiting from intelligence gathered across Atrosec's network.
KEY FEATURES:
Guard adapts to your network architecture, scale requirements, and operational preferences. Choose the deployment model that fits your infrastructure and regulatory environment.

WHAT IT IS: Guard operates in Atrosec's secure cloud infrastructure with network connectivity to your messaging infrastructure. Messages route through Guard for analysis before delivery.
BEST FOR:

WHAT IT IS: Guard components deployed both in cloud (threat
intelligence, dashboard) and on-premises (enforcement points) for optimal performance and data sovereignty.
BEST FOR:

WHAT IT IS: Complete Guard deployment within your data centers
with regular threat intelligence updates. All message processing stays on your infrastructure.
BEST FOR:

See how Guard helps telecom operators block phishing at scale while meeting emerging regulatory obligations globally. Schedule a technical demo with our team.
Or contact our carrier team: telecom@atrosec.com
© 2026 Atrosec. All rights reserved.